Open Source Summit Europe 2018
Edinburgh International Conference Centre
Open Source Summit + ELC Europe 2018: Keynote: Astronomy with Gravitational Waves
Dr. Alexander Nitz
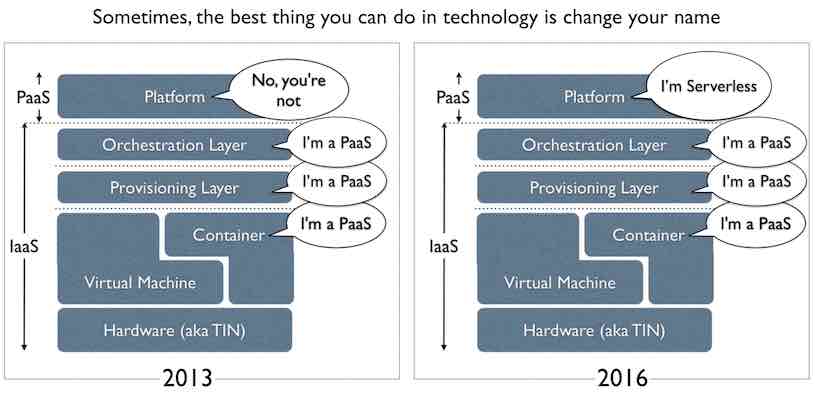
Simon Wardley: The entire history of the PaaS vs Serverless debate, in one simple graphic:
Open Source Summit + ELC Europe 2018: Keynote: Trigger’s Broom, or How I Learned to Stop Worrying and Love Open Source
Dr. Julian Friedman
Open Source Game Design
Brenda Romero
Open Source Banking: End Poverty One Line of Code at a Time
Ed Cable, President & Chief Executive Officer, Mifos Initiative
Using Containers for GPU Workloads (session without slides!)
Christian Brauner
LXD
System containers vs Application containers
Device pass thru routes for VMs
Device node created by kernel Only visible to the host by default Device node handed over to the container
Device node can be handed over to multiple containers if the device supports it. Handing over from one container to another requires a clean-up of the memory. Function-level-reset.
Mknode creates a device node but depends on the user space.
Bind to shared node is propegated into the container.
lxc, no virtualization overhead lxd, deamon to control lxc?
GPU card but also render node, nVidia has different card and node ids.
Nvidia has specific Kernel requirements. Driver and library can be out of sync. GPU is always initialized. Therefore unable to switch to other container (by default). Solution is available by pre-loading the driver and library.
Understanding User Namespaces
Michael Kerrisk
Painting a Picture of the KVM Use-cases in the Container World
Fabian Deutsch, Red Hat
Qemu + KVM = 💪🏻
Containers: focus on applications and user workflows
Problems:
- Container security
- Unable to containerize
Kata containers, add an isolation layer to containers by using an optimized qemu and KVM. Merger of frakti, hypersh and ClearContainers.
Nemu, a forked and optimized qemu and KVM which can be used with Kata Containers or elsewhere. Aims to be a modern hypervisor.
gVisor, adds an isolation layer around containers one option (beyond other) is to use kvm. Proxying syscalls
runq, adds an isolation layer using stock qemu and kvm. Favors simplicity over efficiency.
virtlet, allows you to run VM appliances
KubeVirt, allows you to run VM images using libvirt, qemu and kvm. Guest details in libosinfo.
Testing The Future: Getting Started with Zuul and Ansible
Monty Taylor / Robyn Bergeron, Red Hat

Zuul:
- gated changes
- One or more git repos
- Integrated deliverable
- Testing like deployment
Philosophy:
- all changes flow through code review
- Change only pass if they pass all the tests
- Computers are cheaper than humans
Ramification of Philosophy:
- no direct push access for anyone
- Software should be installed from source
- Testing should be automated and repeatable
- Developers write test with their patches
- Code always works
No tests / manual
Periodic testing
Code Review Systems
- Gerrit
- GitHub (Public and Enterprise)
In work / coming soon:
- GitLab
- BitBucker
Release Management
- Zuul is a CI system
- C stands foor “Continuous”
- It is run Continuously Delivered and Deployed upstream
- Releases are tagged from coode run upstream
- There is no intent too have a ‘stable’ release
- ‘stable’ is a synonym for “old and buggy”
Quick Start
OpenShift
Red Hat
Interactive Learning Portal: learn.openshift.com
eBook O’Reilly: Deploying to OpenShift
Terraform: Sensitive information
- How to handle secrets in state file?
- Terrahelp - https://github.com/opencredo/terrahelp
- Masking, encryption/decription
- Don’t store secrets :) Use:
- AWS/Google Cloud/Azure Key Vault/etc. KMS-like + user-data mechanisms
- AWS System Manager Parameter store
- AWS Secrets manager
- Use resource Roles
- If set master-password for DB service - change it after creation.
- Terrahelp - https://github.com/opencredo/terrahelp
- Secure state at rest using backend built-in encryption
- Secure tfvars and other project/module specific information with:
- pass - The password store - https://www.passwordstore.org/
- git-crypt - https://github.com/AGWA/git-crypt
- .gitignore :)
Source of Knowledge
- Book: “Terraform Up & Running” by Yevgeniy Brikman, https://blog.gruntwork.io
- Hashicorp
- GitHub: Awesome Terraform
- GitHub: Terraform
Tooling
Presentty presentation software uses rst file.
Edward Wilde, ubi-key for private key Hashiconf session sample ubikey session
Probot, 🤖 A framework for building GitHub Apps to automate and improve your workflow.